List of well-known ports used by various peer-to-peer (P2P) protocols. | Download Scientific Diagram

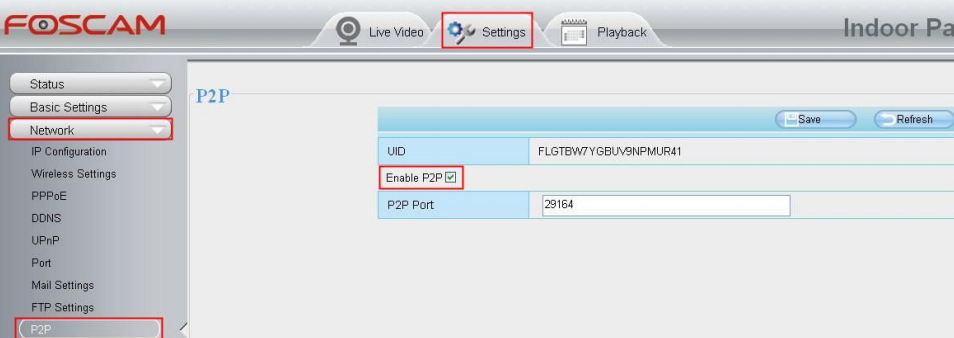
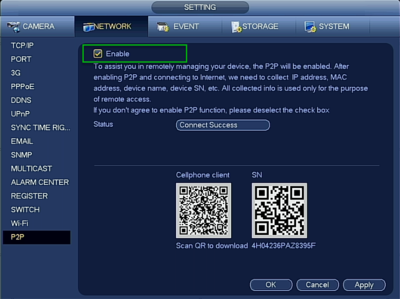
BESDER H.265 16CH 5MP NVR DVR P2P XMEye Security Network Video Recorder 1 SATA HDD Port 4K Output For H.265/264 IP Camera|Surveillance Video Recorder| - AliExpress

How to restrict the ports of p2p connections - Install & Config - Jitsi Community Forum - developers & users
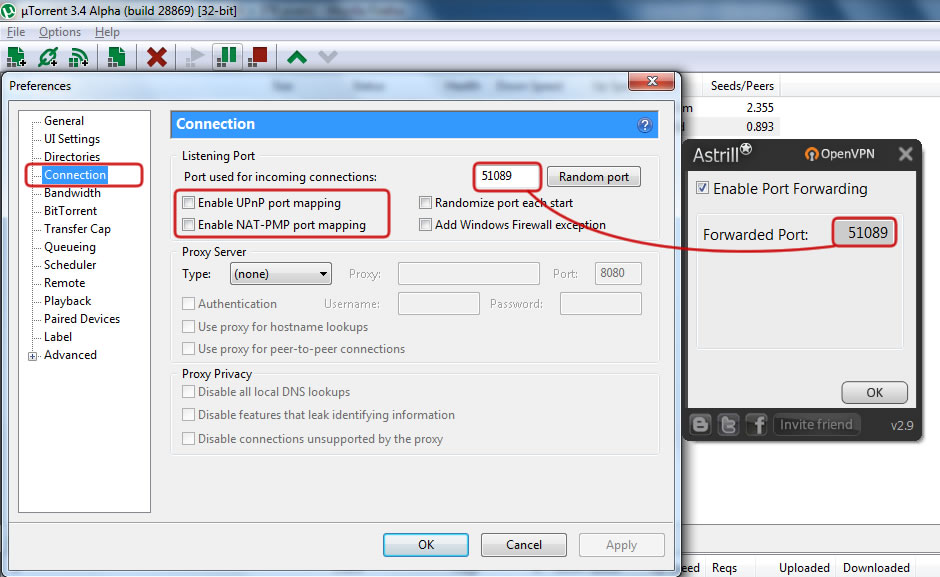
GitHub - selvakn/p2p-port-forward: Command line utility to forward ports between two hosts across different networks/subnets, in a peer-to-peer fashion using zerotier, without sudo privileges

List of well-known ports used by various peer-to-peer (P2P) protocols. | Download Scientific Diagram

A Study of P2P Traversal through Symmetric NAT: with Random Port Assignment: Tsai, ShengQuan: 9783639286304: Amazon.com: Books
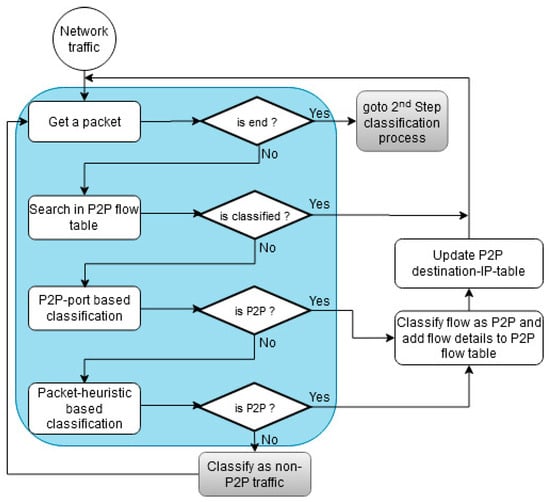
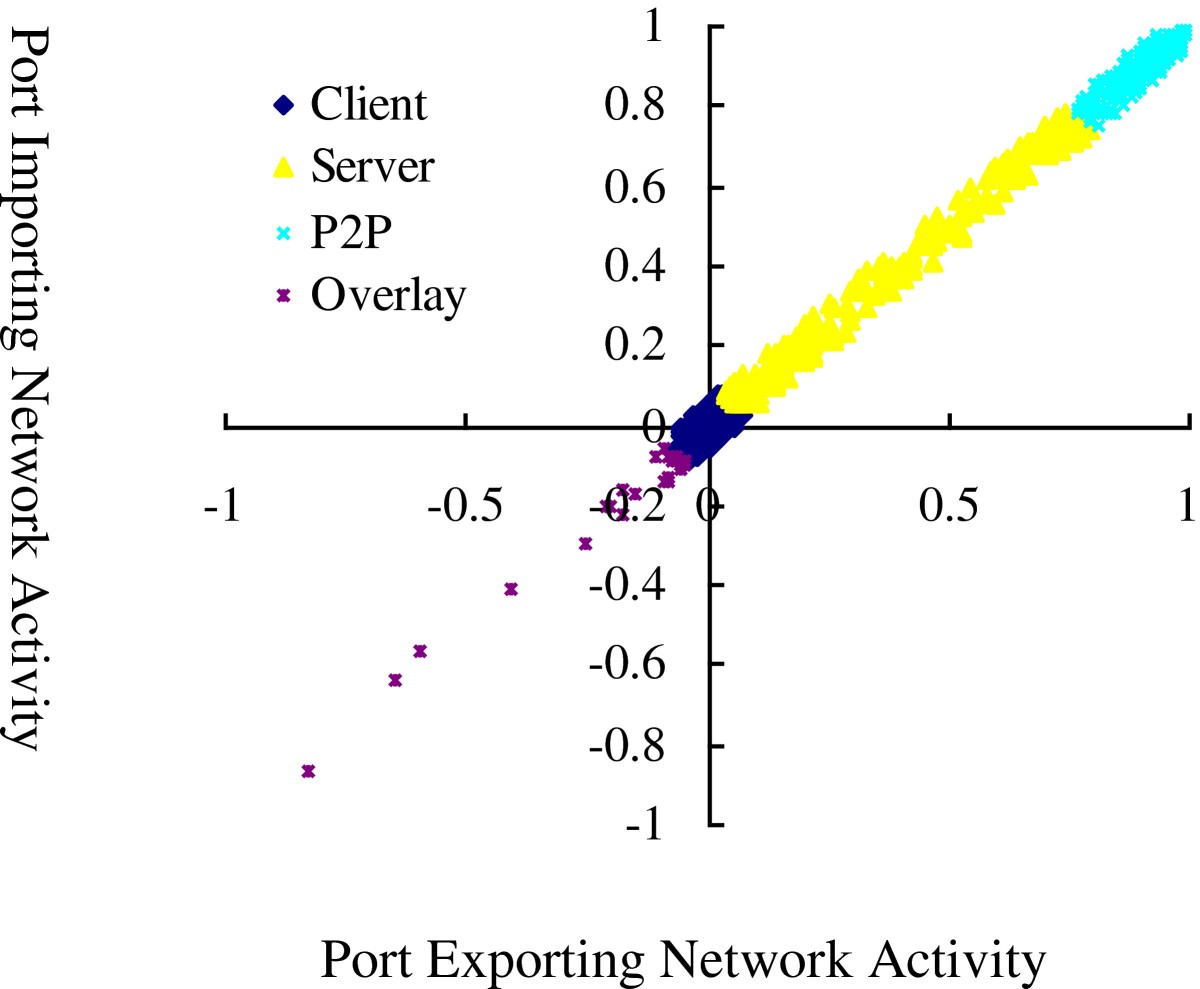
Symmetry | Free Full-Text | Multi-Level P2P Traffic Classification Using Heuristic and Statistical-Based Techniques: A Hybrid Approach
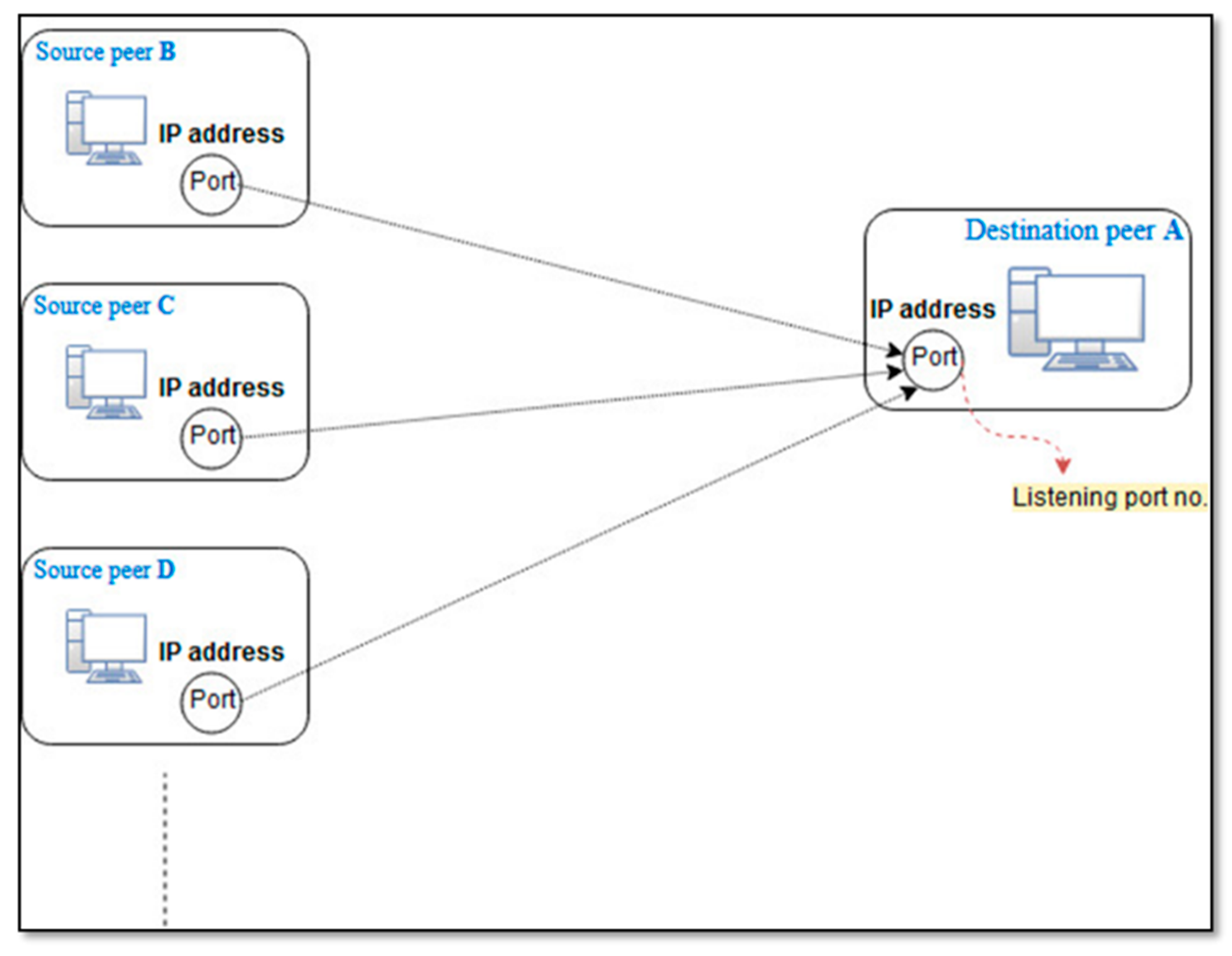
Symmetry | Free Full-Text | Multi-Level P2P Traffic Classification Using Heuristic and Statistical-Based Techniques: A Hybrid Approach